Last updated on: 8th July 2008
Here are some common facts about Windows and Microsoft software product and technology. If you have more facts then tell me or add those in this blog.
1. Dynamic disks are not supported on portable computers or on Windows XP Home Edition-based computers.
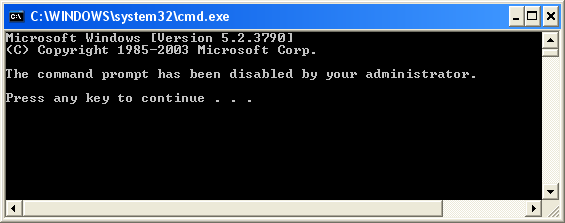
2. In windows XP Home Edition you can’t find gpedit.msc or ntbackup.exe commands because Group Policy and Windows Backup utility are not available.
3. In Windows XP Home Edition “Remote Desktop” Feature is not available.
4. Automated System Recovery is not a supported feature in Windows XP Home Edition using Backup, but Backup is provided on the CD-ROM as additional value to help back up critical system data. To Manually Install the Backup Utility: Double-click the Ntbackup.msi file from the Windows XP Home Edition CD-ROM to start a wizard that installs Backup: CD-ROM Drive:\VALUEADD\MSFT\NTBACKUP. Follow the wizard. When the wizard is complete, click Finish.
5. You cannot format/create a partition more than 32GB as fat 32 file system.
6. You cannot see or access NTFS partitions in Windows 95/98/ME because these operating systems don’t support NTFS file system.
7. You cannot run two Operating System simultaneously from one drive/partition; if you will do this the last operating system you installed on that drive will only run.
8. If you install and run MSN Explorer version 6, your MSN POP3 e-mail account will be migrated to an MSN Hotmail account. If you have Outlook and Outlook Express configured for POP3, you will no longer receive your new MSN e-mail messages.
9. Deleting or reformatting any dynamic disk volume using the Recovery console's DISKPART or FORMAT command or during Windows 2000 text-mode Setup, could result in permanent data loss.
10. You cannot install Windows Vista on FAT/FAT32 file system. Installation of Windows Vista in FAT/FAT32 file system is not supported except NTFS file system.
11. There is no Boot.ini file in Windows Vista. The Boot.ini file is used for legacy Windows versions when dual-booting only.
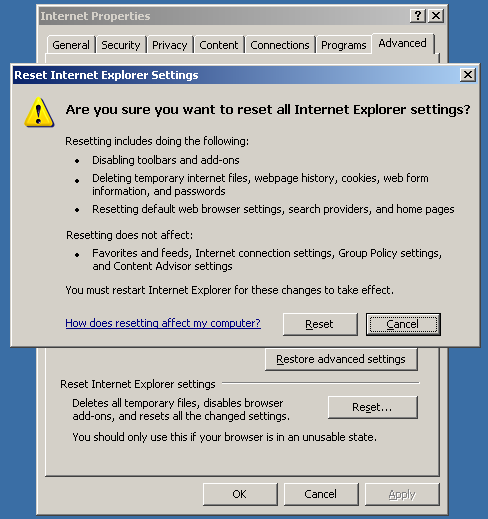
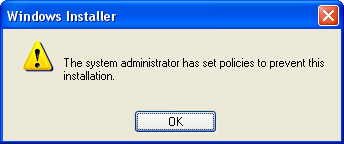
12. You can’t run two or more instances of Windows Installer in Windows XP/2003 Server or lower version of windows. Because running of two or more instances of Windows Installer in Windows Installer v3.1 or lower is not supported. This feature is supported in Windows Installer v4.0 i.e. in Windows Vista or later versions.
13. NetMeeting 3.02 (in Vista) does not support remote desktop sharing. Therefore, the Remote Desktop Sharing option is not available on the Tools menu in NetMeeting 3.02.
14. The default workgroup name in windows XP Home Edition is “MSHome” and in XP Pro, Windows Server 2003 and in Windows Vista it is “WORKGROUP”.
15. The former name of “Microsoft Dynamics products” is “Microsoft Business Solutions”.
16. Windows Server 2008 is the last 32-bit OS from Microsoft. All future operating systems for server hardware from Microsoft beyond Windows Server 2008 will be 64-bit
17. The Fast Saves feature in Word 2003 no longer functions after you install Office 2003 Service Pack 3. The Allow fast saves check box still exists in the Save options in Word 2003. However, the functionality of the option has been disabled. The Fast Saves feature speeds up the saving of a document by saving only the changes that are made to the document. Additionally, documents that are saved when the Fast Saves feature is enabled may contain content that you may not want to share with other people when you distribute the document electronically. This information is known as metadata. Metadata is used for a variety of purposes to improve the editing, the viewing, the filing, and the retrieval of Office files. Because of the design of the Fast Saves feature, text or comments that you delete from a document may remain in the document even after you save the document. Therefore, Microsoft has disabled the functionality of the Fast Saves feature in Office 2003 SP3 to increase the security of Word 2003 documents.
18. Office files that are saved in (e.g. html, mht, rtf, xml) no longer contain the version number of Office after you install Office 2003 Service Pack 3. This is because this behavior was changed in Office 2003 SP3 to improve the security of Office 2003 documents.
19. Upgrading from the following language versions of Windows XP to the matching language of Windows Vista is not supported:
a. Windows XP with the following Language Interface Packs installed: Bulgarian, Croatian, Estonian, Latvian, Lithuanian, Romanian, Serbian-Latin, Slovak, Slovenian, Thai, or Ukrainian.
b. Windows XP Media Center Edition: Traditional Chinese (Hong Kong), Traditional Chinese (Taiwan), Czech, Danish, Finnish, Norwegian (Bokmål), Polish, Portuguese (Portugal), Russian, Spanish, Swedish, or Turkish.
c. Windows XP Tablet PC Edition: Czech, Danish, Dutch, Finnish, Hungarian, Italian, Norwegian, Polish, Portuguese (Brazil), Portuguese (Portugal), Russian, Spanish, Swedish, and Turkish.
If you have one of these operating systems, you will need to perform a clean installation of Windows Vista.
20. The following features are not available in Windows Vista:
a. Active Desktop
b. HyperTerminal
c. Luna visual theme
d. MSN Explorer
e. NetMeeting (replaced with “Windows Meeting Space”)
f. Telnet.exe is no longer installed by default, but is installable feature through “Programs and Features”
g. The network Messenger Service (Winchat.exe)
h. Windows Messenger
i. WinHlp32.exe, used to display 32-bit .hlp files (help pages)
Download PDF version of this article from the link below:
http://www.box.net/shared/i4uuvmar5a
Author: bcdalai
---------------------------------------------------------------------------------